- Webinar |
- USA 2024 |
- Netherlands 2023 |
- USA 2023 |
- Netherlands 2022 |
- USA 2022 |
- Netherlands 2021 |
- USA 2021 |
- Germany 2021 |
- Berlin 2021 |
- Netherlands 2020 |
- Virtual Con 2020 |
- Berlin 2020 |
- Netherlands 2019 |
- USA 2019 |
- Berlin 2019 |
- Netherlands 2018 |
- Berlin 2018 |
- Netherlands 2017 |
- Netherlands 2016 |
- Netherlands 2015
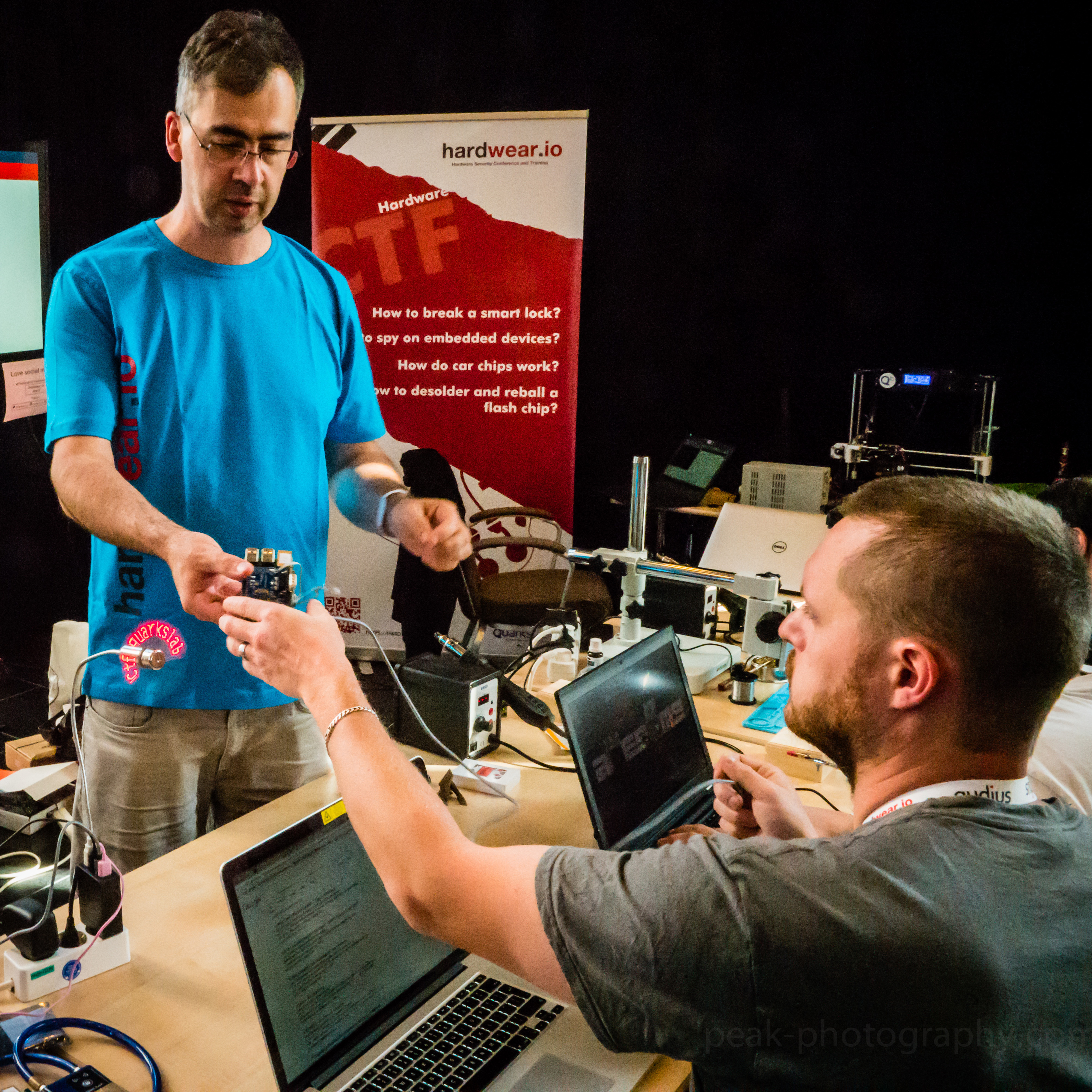
CTF
The Hardware CTF organized by Quarkslab team is coming to the USA edition of hardwear.io as well.
Ever wondered - How to break a smart lock? How to spy on embedded devices? How do car chips work? How to desolder and reball a flash chip?
Then this CTF is for you!
We've got plenty of challenges related to various themes such as RFID, Bluetooth, automotive, side-channel analysis, (de)soldering, radio, and much more. We will provide the hardware hacking tools you might need (soldering iron, logic analyzer, ...) as well as guidance on how to use them.
Just grab your PC and come try to solve our challenges. You'll have fun, learn new skills and who knows, maybe use these skills to break real embedded devices and propose a talk for next year!
Requirements:
A PC with Linux is needed for some of the challenges, but
we've also some other ones that can be done without a PC.
How to Participate:
Once the CTF is open, come to our booth, register a
new team and start playing.
Prizes:
Winner: Chipwisperer,
Saleae Logic,
Jtagulator,
Proxmark3,
Ubertooth,
NoStarch Book &
T-shirt.
First Runner Up: Chipwisperer,
Saleae Logic,
Jtagulator,
Hydrabus + HydraNFC,
NoStarch Book &
Tshirt.
Hardware CTF Sponsor:
Organized by:

hardpwn - Hardware Hacking Contest @hardwear.io USA 2019 #HackFearlessly
13th - 14th June 2019
Second edition of hardpwn contest will be held during hardwear.io conference at Santa Clara, USA. At hardpwn, you will be able to hack fearlessly (vendor is asking you to) and get rewarded. Companies might recruit you if they really like your skills & hacks.
So hackers, bring your hacking machines to hardwear.io and hack fearlessly.
What is the contest?
- We provide hardware devices (target) to the security researchers who have expertise in Side-Channel attacks, RFID/NFC Hacking, Breaking Crypto, Reverse Engineering the Firmware, etc.
- If they find an issue they will report the vulnerability to the OEM directly in a very controlled manner at the conference.
- In return, OEM will reward the researcher with a prize depending on the severity of the finding.
- There would be an NDA signed and the participants would not be allowed to disclose the finding in public till the issue is fixed by the vendor.
For Vendors:
We are open for a Vendors/OEMs willing to test their devices at HardPwn challenge. Your devices will be tested by top security reseachers attending hardwear.io! Interested? Then shoot us an email on info [at] hardwear [dot] io.
Target Devices:
1. Square Terminal
2. Nest Thermostat
3. Nest CameraIQ
4. Nest Guard
5. Nest Detect
6. Google WiFi
7. Google Home Hub
8. Google Home Mini
9. Tapplock
10. SmartThings Hub
Note: To make your hacking experience smoother, we have following hardware hacking tools available at the hardpwn booth (but in limited quantities): JTAGulator, Chipwisperer, Expliot NANO, Hydra Bus, USB Microscope, Rework Station, USB- TTL, Proxmark3, Ubertooth, TNM5000, Jlink, Saleae logic
Contest Prizes:
Prizes will be updated soon.